China to increase protections against hacking in its key industrial sector as it aims to contain major risks by 2026.
Search results for "hacking"
Officials in the US have been sifting through a collective treasure trove of freshly leaked documents from I-SOON casuing a cyber espionage.
In a report published on Wednesday, Microsoft indicated that state-backed Russian, Chinese, and Iranian hackers using AI tools .
Fawry's electronic payment app in Egypt suspended due to hacking fears, causing concerns over customer data.
Security researcher Johann Rehberger's demonstration of AI 'prompt injection' sheds light on the potential for exploitation of AI systems.
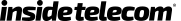
An obscure cloud service company has been providing state-sponsored hackers with internet services to spy on and extort their victims.
Uber Technologies Inc on Friday accepted responsibility for covering up a 2016 data breach that affected 57 million passengers and drivers, as part of a settlement with U.S. prosecutors to avoid criminal charges. In entering a non-prosecution agreement, Uber admitted that its personnel failed to report the November 2016 hacking to the U.S. Federal Trade […]
Discord has surged in popularity in recent years. Once dominated mainly by gamers and other fun groups, and more than a few educational groups, now home to thousands of NFT and crypto enthusiasts who love being part of an exclusive group and engaging with a community. That surge in usage and popularity has also attracted […]
Definition of ethical hacking is the official attempt to gain illegal access to an application, computer system, or data to conduct an ethical hack; it must require replicating actions and strategies of malicious attackers. As such, this practice helps identify security vulnerabilities that can then be resolved before a malicious attacker has the opportunity to […]
While hacking plays a fundamental role in altering the development of systems and networks, ethical hacking is confined within the borders of having an authorized attempt to obtain unsolicited accessibility to the system, application, and even data. What makes ethical hacking “ethical” is the involvement of duplicating strategies and actions of malicious infiltrators, with the sole […]